[ad_1]
Have you ever come throughout conditions the place web sites change into very sluggish to reply? On different days, you may need accessed the identical web sites with none points. What may have led to the delay in loading the web site or accessing its functionalities? The reply would level to DDoS assaults or Distributed Denial of Service assaults. Such sorts of assaults deal with exploiting the setbacks within the design of a web site. The best way wherein blockchain DDoS assaults work exhibits that they’ll result in sluggish efficiency of a web site, and in some instances, it might not even load. Blockchain networks are inherently proof against the Distributed Denial of Service assaults.
DDoS assaults depend on flooding a web site with an awesome quantity of site visitors that will in the end result in the web site crashing. Blockchain is protected from conventional DDoS assaults as a result of the decentralized design excludes the potential of any single level of failure. Nevertheless, you can’t ignore the potential of a blockchain DDoS assault fully due to decentralization.
Hackers wouldn’t flood the community with transaction requests or pings. Quite the opposite, they may go for flooding the blockchain with spam transactions. It might in the end result in congestion within the community that will decelerate the completion of professional transactions. Allow us to be taught extra about DDoS assaults in blockchain and how one can resolve them.
Working of a DDoS Assault
The very first thing it’s worthwhile to be taught earlier than exploring the affect of a DDoS assault in blockchain community is the fundamental definition of a DDoS assault. It refers to any sort of assault that overloads the techniques of a web site with huge quantity of web site visitors. DDoS assaults purpose at bringing the web site down and decreasing its capability for functioning correctly.
Hackers can deploy a DDoS assault by exploitation of bottlenecks within the design of the web site. The method typically includes 1000’s of bots that will hook up with the web site and use bandwidth. The bots would scale back the assets which are out there to precise customers, thereby stopping them from connecting to the web site.
If you wish to know determine DDoS assault, then you will need to find out about the best way wherein it really works. DDoS assaults occur primarily for 2 distinct causes. Initially, hackers can maintain the web site hostage and demand that the web site proprietor ought to pay to cease the assault. Usually, companies have been compelled to pay the ransom to attackers after they couldn’t repair the vulnerability rapidly.
However, DDoS assaults may additionally function an try to have an effect on the popularity of an organization. Malicious rivals can deploy a DDoS assault to showcase that the corporate doesn’t have the assets to counter a DDoS assault. With nearly 20,000 to 30,000 DDoS assaults occurring on daily basis, you will need to discover efficient methods to resolve them.
Construct your id as a licensed blockchain knowledgeable with 101 Blockchains’ Blockchain Certifications designed to offer enhanced profession prospects.
Variants of DDoS Assaults
The following necessary factor it’s worthwhile to be taught for exploring the affect of DDoS assaults in blockchain networks is the sorts of DDoS assaults. Yow will discover several types of assaults, together with layer 4 DDoS assaults that may goal completely different bottlenecks in a web site. A few of the frequent DDoS assaults embrace volumetric assaults, software assaults, protocol assaults, TCP connection assaults, and fragmentation assaults. Right here is an outline of the affect of the completely different DDoS assaults on a web site.
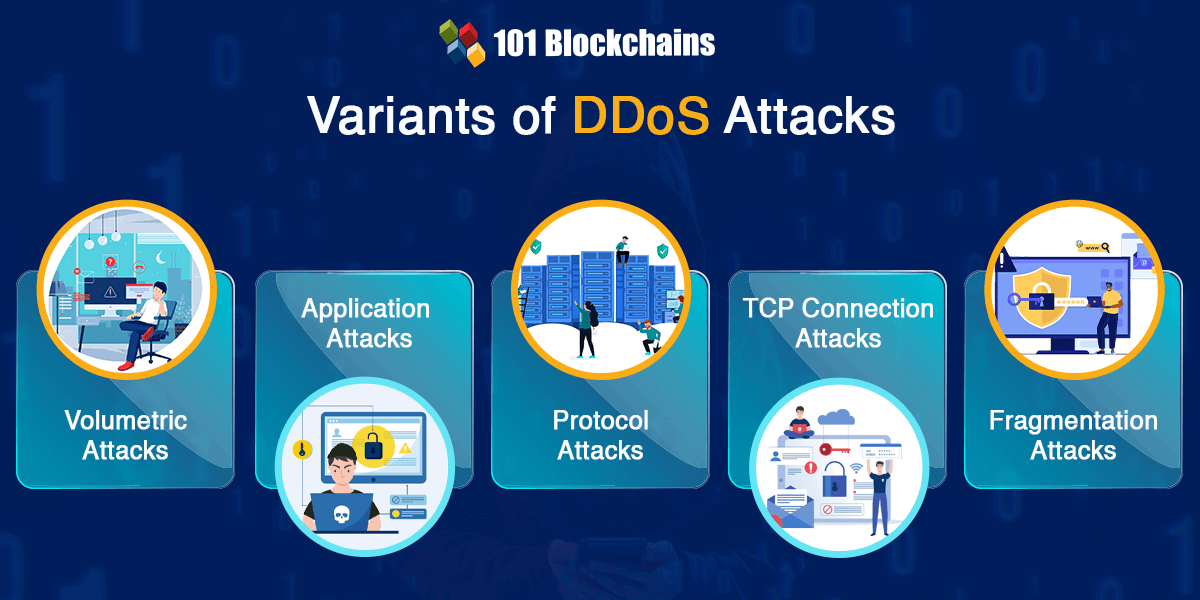
Volumetric assaults purpose at consuming the bandwidth inside the goal community or service or between the goal community or service and the remainder of the web. The first goal of volumetric assaults revolves round guaranteeing congestion. Volumetric assaults devour bandwidth and result in difficulties in connection between a web site and the web.
Utility assaults are additionally one other necessary variant of DDoS assaults. You possibly can perceive the affect of DDoS assault in blockchain community by figuring out how software assaults goal the appliance quite than the encircling infrastructure. Some of the alarming features of software assaults is the truth that you wouldn’t want highly effective techniques. Hackers can deploy software layer assaults by utilizing smaller techniques with decrease computing energy.
Protocol assaults work by affecting the power of the community to finish features. For instance, hackers may ship incomplete knowledge or packets of knowledge. The unfinished packets could lead on the server to attend to obtain the remaining knowledge or connection requests.
One other notable variant of DDoS assaults factors at TCP connection assaults which deal with occupying connections. TCP connection assaults devour all of the out there connections to infrastructure units, together with software servers, load balancers, and firewalls. On high of it, units which are able to sustaining state throughout tens of millions of connections is also weak to such assaults.
-
Fragmentation Assaults
Fragmentation assaults deal with utilizing packets of knowledge transmitted to web sites. The web site receives a sudden surge in fragmented knowledge. The system should reassemble the fragments to course of the information or request. Nevertheless, sending extra knowledge in packets may hamper the power of internet sites to assemble the information, thereby decreasing the efficiency.
Begin studying Blockchain with World’s first Blockchain Ability Paths with high quality assets tailor-made by business specialists Now!
How Can You Establish DDoS Assaults?
The best strategy for locating solutions to “Why are DDoS assaults growing in blockchain?” would additionally contain figuring out DDoS assaults. Some of the frequent signs of a DDoS assault is the unavailability of a web site or service. Nevertheless, you may as well discover different signs, comparable to efficiency points or professional spikes in web site site visitors. You should use penetration testing for a protected and complete assault simulation that may expose advanced vulnerabilities. A few of the in style penetration testing site visitors analytics instruments may assist in recognizing the indicators of a DDoS assault.
DDoS assaults may be recognized within the type of suspicious site visitors coming from a single IP vary or IP tackle. You may also discover determine DDoS assault by checking for unexplained surges in requests to a single endpoint or web page. DDoS assaults may additionally take the type of a surge in site visitors from customers who’ve an analogous behavioral profile, comparable to internet browser model, gadget sort, or geolocation. One other notable signal of DDoS assaults is seen in odd site visitors patterns, comparable to spikes in site visitors at odd hours or rare spikes.
You must also discover that DDoS assaults additionally showcase completely different indicators based on sophistication and size. DDoS assaults could possibly be long-term assaults or burst assaults. With the rise of IoT know-how and highly effective computing units, the assets for producing extra volumetric site visitors have been growing. Due to this fact, attackers may create larger site visitors quantity in shorter durations. Yow will discover that burst assaults are troublesome to detect as they solely final for just a few seconds or a minute.
What’s DDoS in Blockchain?
You possibly can find out how blockchain DDoS assaults work by understanding how blockchain know-how works. Probably the most distinguished spotlight of blockchain networks is decentralization by design. Blockchain networks have just a few or 1000’s of nodes engaged on verification of transactions. Customers would submit transactions on the community, and all of the nodes would work collectively to validate the transaction. The decentralized design ensures {that a} conventional DDoS assault would solely obtain success in compromising one or few nodes. Nevertheless, it might not have an effect on the community as all the opposite nodes proceed their operations.
With the decentralized design, blockchain networks are proof against conventional DDoS assaults. Nevertheless, it doesn’t make them fully proof against DDoS assaults. Several types of blockchain networks have completely different ranges of resistance in direction of DDoS assaults. Yow will discover the reason for layer 4 DDoS assaults by exploring various factors.
The components embrace the variety of nodes chargeable for validation of transactions within the blockchain community, node shopper variety, complete community hash fee, and confidentiality of validator schedule. For instance, a blockchain community with few nodes that run the identical shopper can be extra weak to DDoS assaults. Quite the opposite, a blockchain community with 1000’s of nodes and working completely different shoppers can be extra proof against DDoS assaults.
Get acquainted with the phrases associated to blockchain with Blockchain Fundamentals Flashcards.
How Do DDoS Assaults Manifest in Blockchain Networks?
DDoS assaults in blockchain networks emphasize compromises within the protocol layer quite than attacking the person nodes. The 2 frequent methods to deploy a DDoS assault in blockchain community embrace good contracts assaults and transaction flooding. Right here is an outline of the 2 distinguished methods wherein you could find DDoS assaults in blockchain networks.
Transaction flooding is among the commonest variants of DDoS assaults in blockchain. Many of the blockchain networks have a hard and fast block dimension. Each block has a selected higher restrict for the variety of transactions it may possibly handle. You will need to word that blocks in a blockchain community are produced at pre-defined intervals. The pending transactions that can’t discover a place within the present block would go into the mempool of a blockchain. The transactions would stay within the mempool till they’re verified and included within the subsequent blocks.
Hackers can implement a blockchain DDoS assault by transaction flooding by spamming the community with incomplete transactions. In consequence, it might forestall the affirmation of professional transactions, which might go into the mempool. The assault would assist in slowing down the operations of the blockchain community and legit customers must pay an especially excessive price for validating their transactions.
Hackers may additionally implement a DDoS assault by good contract hacking. Such sorts of assaults would solely have an effect on blockchain networks that supply assist for good contracts. Totally different blockchain networks have completely different ranges of resistance to such assaults. You may also discover an evidence for questions like ‘Why are DDoS assaults growing in blockchain?’ within the repeatedly rising utilization of good contracts. Hackers may perform a DDoS assault by sending a transaction that requires consumption of extra computing assets. In consequence, the community couldn’t add different professional transactions, thereby resulting in outcomes much like transaction flooding.
Excited to be taught in regards to the vital vulnerabilities and safety dangers in good contract growth, Enroll now within the Good Contracts Safety Course
Impact of Blockchain DDoS assaults
The evaluate of the 2 distinguished methods wherein hackers may implement DDoS assaults in blockchains exhibits that the assaults forestall the addition of latest transactions. Nevertheless, you’ll be able to be taught determine DDoS assault for blockchain networks by checking for different indicators. Blockchain DDoS assaults may additionally result in the next outcomes.
Blockchain networks observe a peer-to-peer mannequin wherein each node receives a block or transaction and sends a duplicate to all neighbors. All of the nodes would obtain completely different copies of similar transaction. Because the transaction flooding results in extra transaction quantity, it might eat up the community bandwidth thereby resulting in congestion.
The affect of a blockchain DDoS assault can be seen in the way it results in node failures. Nodes must take care of an especially excessive variety of transactions, which might put stress on the reminiscence or CPU and will crash.
Wish to discover an in-depth understanding of safety threats in DeFi initiatives? Enroll now within the DeFi Safety Fundamentals Course
How Can You Stop Blockchain DDoS Assaults?
One of the best strategy for guaranteeing safety in opposition to blockchain DDoS assaults includes growing the size of decentralization. However, the method of reaching decentralization would take extra time. Due to this fact, it is best to select efficient safeguards to keep away from the blockchain community turning into a sufferer of DDoS assaults. You will need to be certain that all nodes on the community have sufficient storage, community bandwidth, and processing energy. You must also determine and exclude potential spam transactions from the blocks which are more likely to devour extra computation assets.
Begin your journey to turning into an knowledgeable in Web3 safety with the steering of business specialists with Web3 Safety Professional Profession Path
Conclusion
The rising quantity of DDoS assaults in blockchain has created a notable concern for companies looking for blockchain as a device for digital transformation. On the similar time, you will need to word that it’s inconceivable to realize full immunity in opposition to blockchain DDoS assaults. You possibly can determine the options for DDoS assaults by studying how blockchain DDoS assaults work and the most effective practices for diagnosing the indicators.
Malicious actors may implement DDoS assaults by transaction flooding and assaults on good contracts. Nevertheless, you’ll be able to guarantee security in opposition to DDoS assaults in blockchain networks by constructing safe good contracts. On high of it, you may as well depend on optimization of the nodes with higher community bandwidth, storage, and processing energy for dealing with DDoS assaults. Be taught extra about web3 safety and the options for blockchain DDoS assaults proper now.
*Disclaimer: The article shouldn’t be taken as, and isn’t supposed to offer any funding recommendation. Claims made on this article don’t represent funding recommendation and shouldn’t be taken as such. 101 Blockchains shall not be chargeable for any loss sustained by any one who depends on this text. Do your personal analysis!
[ad_2]