
[ad_1]
It supplies an revolutionary and user-friendly solution to rework the expertise of customers with on-line providers and options. The solutions to “Is Web3 susceptible?” draw the limelight in the direction of the benefits it brings to the tech panorama. There is no such thing as a solution to deny that Web3 has the potential to rework on-line experiences with decentralization and thru empowering customers.
However, Web3 safety dangers have additionally been rising by way of their financial influence. Apparently, greater than 167 main assaults within the area of Web3 in 2022 resulted in approximate losses of virtually $3.6 billion. Inside the first half of 2022, Web3 safety hacks resulted in losses value over $2 billion, which is greater than all losses in 2021. Due to this fact, consciousness concerning essential vulnerabilities in Web3 safety is an important requirement for Web3 builders and founders. The next submit supplies you with a quick information to challenges with distinguished Web3 vulnerabilities and their options.
Fundamentals of Web3
Web3 is an revolutionary transformation within the primary construction of the net with new options based mostly on blockchain expertise. Consultants describe Web3 because the decentralized web, which might be developed over decentralized blockchains utilized in cryptocurrency networks, equivalent to Ether and Bitcoin.
The sort of vulnerability in Web3 is without doubt one of the distinguished considerations, contemplating the truth that web sites and apps in Web3 can handle knowledge in intuitive methods, similar to people. As well as, Web3 wouldn’t depend on blockchain expertise solely. The opposite applied sciences related to Web3 embrace machine studying, distributed ledger expertise or DLT, and massive knowledge.
Web3 envisions an open, clever, and autonomous web. One of many vital highlights in favor of Web3 factors to the reassurance of person management. Web3 ensures customers have full management over their knowledge, digital belongings, and digital identities.
Need to develop into a Cryptocurrency skilled? Enroll Now in Cryptocurrency Fundamentals Course
Why Do You Must Know the Web3 Vulnerabilities?
The necessity for studying about Web3 vulnerabilities has been gaining distinguished ranges of consideration in current occasions. Widespread responses to ‘what’s a vulnerability in safety’ would discuss with potential areas of assault. Within the case of Web3, the distinguished highlights concentrate on the enhancements launched by Web3. However, you will need to perceive how Web3 supplies safety. On the identical time, you must also concentrate on studying in regards to the notable safety threats which haven’t been addressed within the current Web3 structure.
Developments within the Web3 area are repeatedly increasing, particularly within the case of metaverse and NFT collections. Nevertheless, it’s also vital to surprise how Web3 presents higher safety than Web3. The doubts concerning varieties of safety vulnerabilities in Web3 emerge from the threats to Web3 tasks.
For instance, an assault on the Wormhole Bridge resulted in losses value over $360 million. Apparently, a hacker had exploited a vulnerability within the design of the sensible contract perform of the bridge to the Solana blockchain. Due to this fact, consciousness concerning Web3 vulnerabilities is an important requirement for enhancing belief within the Web3 ecosystem.
What are Web3 Vulnerabilities?
Earlier than figuring out essentially the most noticeable vulnerabilities in Web3 tasks, it’s good to perceive the definition of vulnerabilities. The issue with vulnerability in cyber safety for Web3 options is the sophisticated nature of vulnerabilities. Web3 tasks have led to an unprecedented rise within the variety of safety points. The most important downside in making certain Web3 safety focuses on the difficulty of acquiring the assistance of specialists. Whereas bug bounty packages serve efficient leads to the identification of Web3 vulnerabilities, many cybersecurity professionals dismiss Web3 and blockchain as scams.
Web3 vulnerabilities are step by step turning into troublesome considerations for Web3 tasks. The variety of Web3 purposes based mostly on blockchain expertise continues to rise and will increase the floor space for hackers. As a matter of reality, Web3 safety dangers characteristic similarities to standard cybersecurity points. Permissionless environments and potentialities of bugs in sensible contract code current favorable components for compromises in sensible contract functionalities. Due to this fact, you will need to evaluate essentially the most impactful Web3 vulnerabilities, their challenges, and the related options.
Construct your id as an authorized blockchain skilled with 101 Blockchains’ Blockchain Certifications designed to offer enhanced profession prospects.
Most In style Web3 Vulnerabilities
An in depth understanding of responses to ‘what’s a vulnerability in cyber safety’ would assist you to establish the traditional issues for cybersecurity. However, the potential similarities between Web3 vulnerabilities and conventional safety dangers present higher flexibility for understanding the safety dangers in Web3. Right here is a top level view of essentially the most distinguished Web3 vulnerabilities you need to be careful for in 2023.
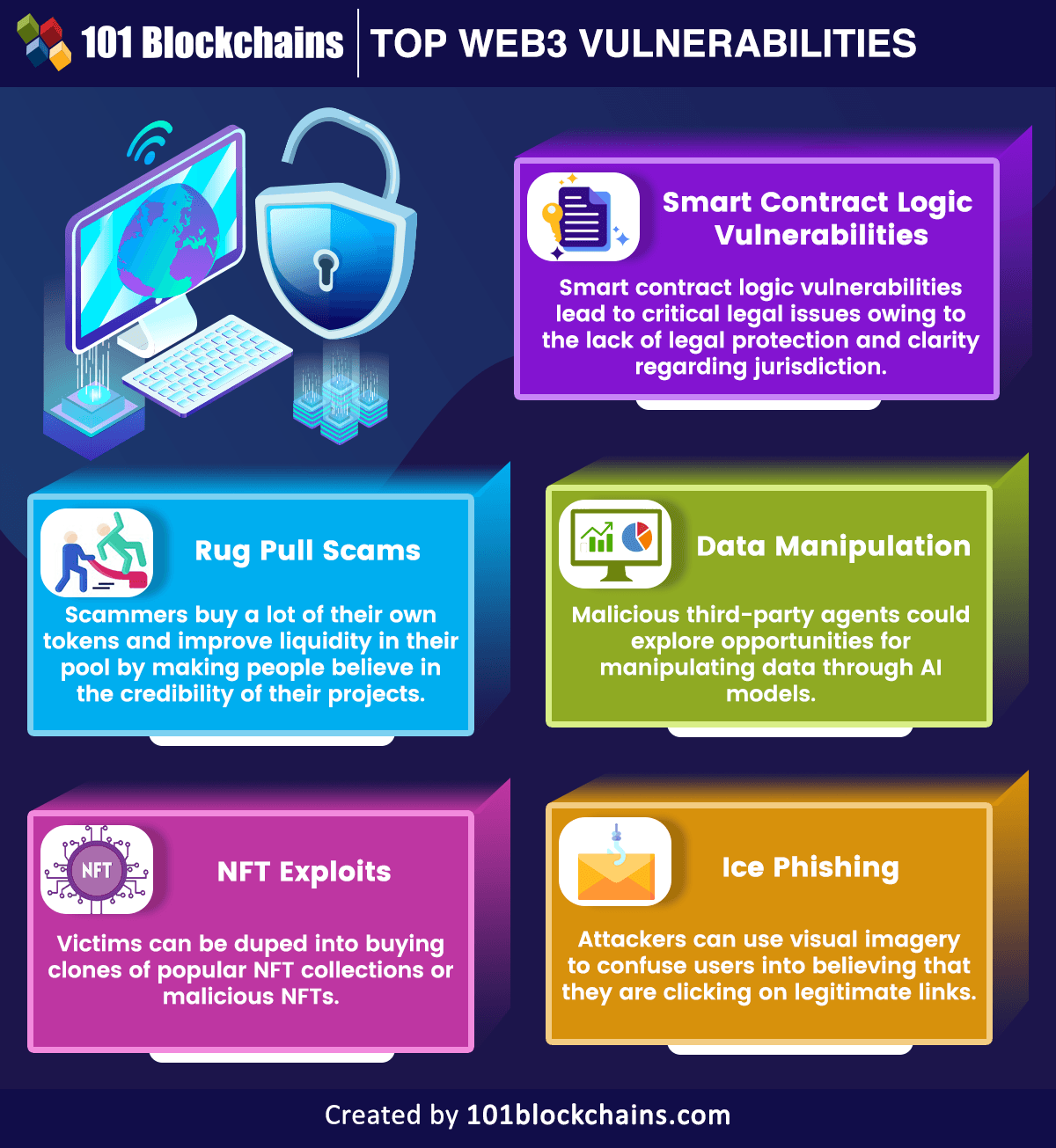
Please embrace attribution to 101blockchains.com with this graphic. <a href="https://101blockchains.com/blockchain-infographics/"> <img src="https://101blockchains.com/wp-content/uploads/2023/04/High-Web3-Vulnerabilities-1.png" alt="High Web3 Vulnerabilities="0' /> </a>
Curious to develop an in-depth understanding of web3 software structure? Be part of Yearly/Yearly+ Plan and Enroll Now in Web3 Utility Improvement Course!
Sensible Contract Logic Vulnerabilities
The use instances of sensible contracts in Web3 have opened up the roads for creating many revolutionary purposes. On the identical time, sensible contracts have emerged as one of many high Web3 vulnerabilities owing to faults within the software logic. Sensible contracts outline the specs of an settlement in a contract with code and work in line with the outlined logic.
-
Challenges with Sensible Contracts
The issue with sensible contracts is that they should be deployed on a blockchain community for desired operations. The presence of sensible contracts on decentralized blockchain networks implies that the safety of sensible contract knowledge relies on the safety of the underlying blockchain.
The varieties of safety vulnerabilities in sensible contracts emerge from the problems within the logic of the sensible contracts. Logic hacks on sensible contracts have been applied for exploiting varied options and providers in Web3 tasks. On high of it, sensible contract logic vulnerabilities may also result in essential authorized points owing to the dearth of authorized safety and readability concerning jurisdiction.
-
Options for Sensible Contract Vulnerabilities
The options for addressing vulnerabilities with sensible contracts would revolve round cautious analysis of the character of blockchain and sensible contracts. Cautious analysis of the blockchain and sensible contracts all through completely different levels, from planning to the testing section, might help in reviewing all blockchain traits. You may tackle sensible contract vulnerabilities and the related Web3 safety dangers by studying about blockchain and sensible contract programming.
Curious to grasp the entire sensible contract growth lifecycle? Be part of Yearly/Yearly+ Plan and get free entry to the Sensible Contracts Improvement Course Now!
Rug Pull Scams
One other distinguished addition amongst vulnerabilities within the Web3 panorama refers to rug pull scams. Rug pulls scams discuss with occasions during which malicious Web3 builders abandon a mission after getting access to large chunks of investor wealth. The definition of rug pull vulnerability in cyber safety is much like Ponzi schemes in the actual world. A gaggle of builders created a Web3 mission and a local token that’s listed on decentralized exchanges in pair with widespread cryptocurrencies equivalent to Ethereum.
-
Challenges with Rug Pull Scams
Probably the most distinguished problem with rug pull scams is the truth that you don’t get a whiff of foul play earlier than it’s late. Rug pulls scammers to start out by creating hype round their mission on Twitter, Telegram, and completely different social media platforms. Some rug-pull scams additionally rent influencers to make folks consider within the credibility of the mission.
As well as, the scammers purchase a whole lot of their very own tokens and enhance liquidity of their pool, thereby incomes the religion of traders. The issue with such a sort of vulnerability in Web3 turns into extra sophisticated with the benefit of itemizing tokens with none prices on decentralized exchanges.
-
Options for Rug Pull Scams
The advisable answer for avoiding losses resulting from rug pull scams is due diligence. You should make investments efforts in complete analysis a few Web3 mission earlier than investing your cash in it. Ranging from the token pool to the main points of the founders and roadmap of the mission, it’s good to evaluate completely different points of Web3 tasks to keep away from the dangers of rug pull scams.
Excited to study the fundamental and superior ideas of ethereum expertise? Enroll Now in The Full Ethereum Expertise Course
NFT Exploits
NFTs or non-fungible tokens are additionally different frequent targets of Web3 safety threats. Non-fungible tokens play an important function in driving the mainstream adoption of cryptocurrencies and inspiring the acceptance of Web3. NFTs can serve a number of use instances apart from defining distinctive proofs of asset possession.
-
Challenges with NFT Safety
The responses to “Is Web3 susceptible?” with respect to NFTs would additionally concentrate on sensible contracts, which outline the possession report of NFTs. Non-fungible tokens are a relatively new expertise, thereby implying the need for familiarizing themselves with challenges to their safety. For instance, victims might be duped into shopping for clones of widespread NFT collections or malicious NFTs. Just one click on on a hyperlink for a malicious NFT can grant full entry to your NFT assortment or crypto belongings.
-
Options for NFT Safety
The identification of vulnerability in cyber safety for non-fungible tokens doesn’t recommend that you shouldn’t use NFTs. Quite the opposite, it’s good to search for higher options that may assist you to develop a complete understanding of vulnerabilities in NFT sensible contracts. Moreover, you may as well leverage alerts and notifications for suspicious actions in NFT marketplaces to keep away from safety dangers.
Information Manipulation
One other distinguished concern in Web3 safety factors to the probabilities of information manipulation in dApps, that are a significant element of the Web3 panorama. Decentralized purposes depend on peer-to-peer networks and distributed codebase, which helps in storing knowledge.
-
Challenges of Information Manipulation
AI is without doubt one of the very important applied sciences within the Web3 panorama, and you will discover many dApps and sensible contracts utilizing synthetic intelligence. The AI fashions want massive quantities of high-quality knowledge for coaching on a selected matter. With out satisfactory safeguards for dApps or sensible contracts, malicious third-party brokers might discover alternatives for manipulating knowledge via AI fashions.
-
Answer for Information Manipulation
The options for Web3 safety dangers with knowledge manipulation level on the collection of safe blockchains for deploying dApps.
Construct your fluency in Web3 and develop decentralized options with the world’s first Web3 Knowledgeable Profession Path with high quality sources tailor-made by business consultants Now!
Ice Phishing
The checklist of distinguished Web3 safety vulnerabilities additionally consists of ice phishing as a current addition. It focuses on using misleading strategies for duping customers into signing malicious transactions, which grant permissions to the attackers to make the most of the person’s tokens. The origins of ice phishing emerge from the power of delegation of token utilization permissions.
-
Challenges in Ice Phishing
Ice Phishing strategies are one of the crucial harmful varieties of safety vulnerabilities in Web3 as they concentrate on social engineering assaults. Attackers can use visible imagery to confuse customers into believing that they’re clicking on respectable hyperlinks.
-
Options to Ice Phishing
The answer to ice phishing factors to the need of safety coaching. Web3 customers should observe the most effective practices for interacting with emails and double-check earlier than clicking on hyperlinks. It is best to take note of the logos, web site URL, and mission identify fastidiously to keep away from problems with ice phishing.
Study the basics, challenges and use instances of Web3.0 blockchain from the E-book: AN INTRODUCTION TO WEB 3.0 BLOCKCHAIN
Conclusion
The define of the notable vulnerabilities in Web3 proves that Web3 will not be as safe as everybody imagined. It’s a new technological idea and has its justifiable share of setbacks in safety. Most vital of all, the high Web3 vulnerabilities concentrate on figuring out areas of assault that may generate handy outcomes for attackers. For instance, a easy error within the sensible contract code can result in losses of tens of millions of {dollars}. Due to this fact, analysis on Web3 vulnerabilities could be a significant requirement for supporting the adoption of Web3 sooner or later.
*Disclaimer: The article shouldn’t be taken as, and isn’t supposed to offer any funding recommendation. Claims made on this article don’t represent funding recommendation and shouldn’t be taken as such. 101 Blockchains shall not be accountable for any loss sustained by any one who depends on this text. Do your individual analysis!
[ad_2]



